
HID
Global Identity & Access Control Solutions
Secure Credential, Reader & Authentication Technologies for Enterprise Access Control in Europe

HID Global develops secure credential and reader technologies used in enterprise and regulated access control infrastructures across Europe.
As an official HID partner, Intertec supplies HID credential and reader solutions for professional system integrators and enterprise projects requiring secure identity validation and long-term deployment stability.
HID technologies focus on encrypted credential ecosystems, multi-technology RFID readers, secure communication protocols, and identity authentication platforms designed for scalable access control environments.
What HID Technologies Represent in Access Control Architecture
Within a modern access control system, HID operates primarily in the secure identity and credential validation layer.
HID solutions typically cover:
- Encrypted RFID smart credentials
- Secure reader-based authentication
- OSDP Secure Channel communication
- Mobile credential validation
- Physical and logical identity convergence
HID SEOS® is an encrypted credential technology based on a Secure Identity Object architecture that enables portable, cryptographically protected identities across physical and digital environments.
HID is widely specified when credential encryption, lifecycle control, and interoperability within enterprise access control platforms are core project requirements.
Core Credential Technologies

HID credential platforms are structured around secure smart card standards and encrypted communication models.
Technologies commonly deployed in European access control projects include:
- iCLASS SE® secure credential platform
- SEOS® (Secure Identity Object™)
- MIFARE DESFire EV2 / EV3 compatibility
- ISO/IEC 14443 compliant smart credentials
- ISO/IEC 7816 smart card architecture
- Secure mobile credential frameworks
iCLASS SE® enables mutual authentication and encrypted data exchange between credential and reader, supporting AES-based cryptographic protection and diversified key management.
These technologies support:
- Protection against credential cloning
- Secure key diversification models
- Controlled credential lifecycle governance
- Migration from legacy proximity systems to encrypted smart credentials
HID is frequently specified in modernization projects replacing 125 kHz proximity credentials with secure 13.56 MHz smart card infrastructures.
Multi-Technology Reader Platforms
HID reader platforms are designed for interoperability and phased credential migration.
Professional deployment capabilities include:
- Dual-frequency support (125 kHz + 13.56 MHz)
- Compatibility with iCLASS, DESFire, SEOS and additional credential formats
- NFC and mobile credential readiness
- OSDP Secure Channel support
- Encrypted reader-to-controller communication
- Indoor and outdoor-rated models
OSDP Secure Channel is a standards-based encrypted communication protocol between reader and controller that mitigates interception and replay risks in professional access control systems.
This architecture allows integrators to deploy multi-technology readers during transition phases while maintaining operational continuity.
Authentication & Identity Convergence
HID technologies extend beyond physical access validation.
Enterprise deployments may include:
- FIDO2-ready authentication tokens
- Smart credential-based workstation authentication
- Converged physical and logical access policies
- Integration with identity management platforms
This supports alignment between physical security infrastructure and enterprise IT identity governance frameworks.
Typical HID Deployment Scenarios in Europe
HID technologies are commonly specified in environments requiring secure credential governance and scalable access control infrastructure.
Typical deployment sectors include:
- Corporate headquarters and campus environments
- Healthcare and pharmaceutical facilities
- Financial institutions
- Government infrastructure
- Energy and critical infrastructure
- Data centers
HID platforms are frequently integrated within multi-vendor access control ecosystems rather than limited to proprietary system architectures.
HID Access Control Architecture Overview
HID technologies operate within the secure identity validation path of enterprise access control architectures.
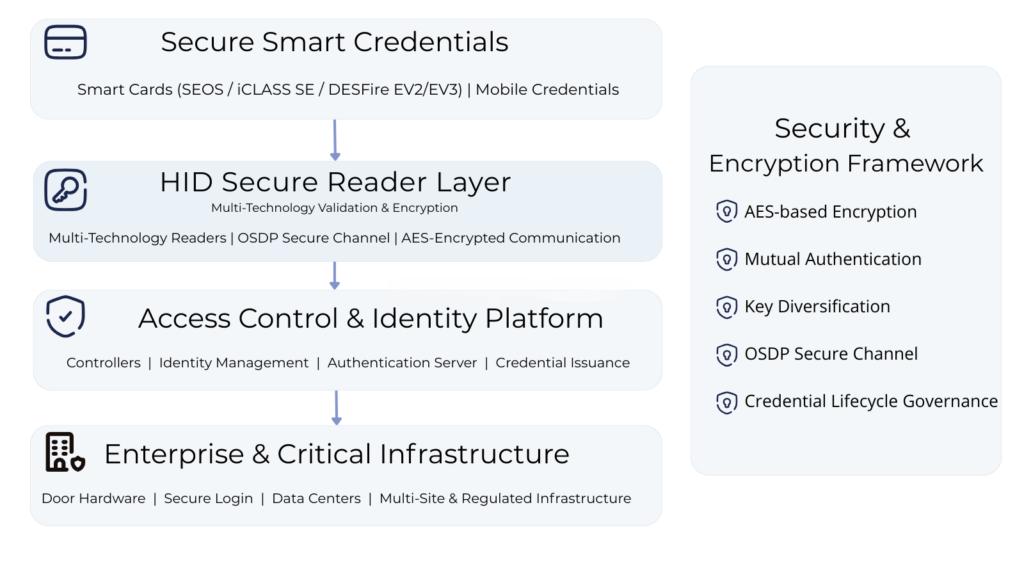
HID components may operate:
- Within full HID credential ecosystems
- In third-party controller environments
- In phased credential migration architectures
- In converged physical and logical identity deployments
Standards-based communication and encrypted credential authentication ensure secure interoperability across multi-vendor enterprise access control infrastructures.
HID technologies operate within enterprise access control ecosystems that combine credential validation, controller logic, and enforcement infrastructure. For a broader view of system architectures and deployment models, refer to our Access Control Systems overview.
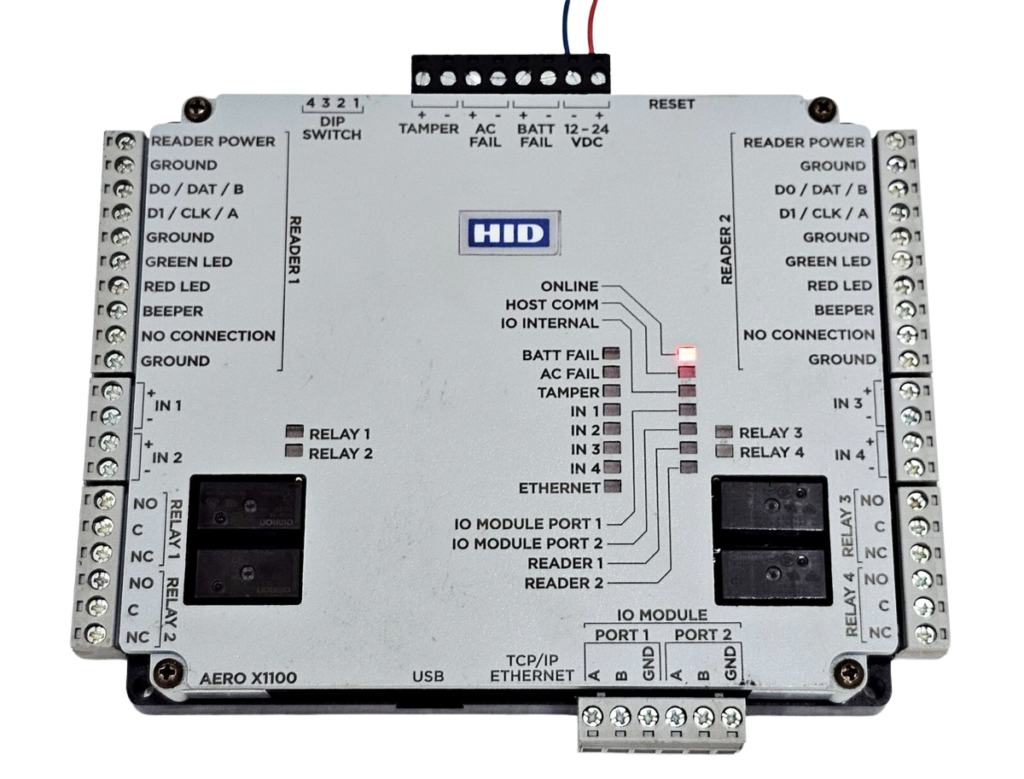
HID secure readers are typically integrated into controller-based platforms such as Rosslare, where encrypted credential authentication connects directly to door-level enforcement and access decision workflows.
Credential Migration & Modernization Strategy
European projects frequently require modernization of legacy access control credentials.
HID migration strategies support:
- Parallel acceptance of legacy and secure credentials
- Multi-technology reader deployment
- Gradual introduction of encrypted smart credentials
- Integration of mobile credentials alongside physical cards
- Controlled transition without full infrastructure replacement
This approach reduces project risk while improving overall credential security posture.
In enterprise deployments, HID secure credential technologies may operate alongside dedicated credential enrollment and interface platforms such as ACS, particularly in workstation-based issuance and identity enrollment environments.
Security & Compliance Considerations
European projects frequently require modernization of legacy access control credentials.
HID migration strategies support:
- Parallel acceptance of legacy and secure credentials
- Multi-technology reader deployment
- Gradual introduction of encrypted smart credentials
- Integration of mobile credentials alongside physical cards
- Controlled transition without full infrastructure replacement
These elements align with modern European enterprise security and data governance requirements.
HID Solutions Distribution & Technical Support
Intertec supplies HID credential and reader technologies for professional access control projects across Europe.
Technical support includes:
- Credential and reader compatibility consultation
- Migration strategy coordination
- Access control architecture alignment
- Integration support within multi-vendor environments
For technical specification guidance or project-level consultation regarding HID access control solutions, contact our team.
ABOUT INTERTEC
Intertec is a distributor of access control, intercom and identification systems for installers, system integrators and security professionals across Estonia, Latvia and the European market.


